Both TLS and SSL are protocols that help you authenticate and transport data securely over the Internet. But what’s the difference between TLS vs SSL? And is it something you should worry about?
In this article, you’ll learn the key differences between TLS and SSL, as well as how both protocols connect to HTTPS. You’ll also learn why, as an end user, you probably don’t have to worry too much about TLS vs SSL or whether you’re using an “SSL certificate” or a “TLS certificate.”
You can click below to skip to a specific section or read the entire article:
What’s the difference between TLS vs SSL? How TLS and SSL work at a basic level Why is it called an SSL certificate and not
- a TLS certificate? Why
- (and Why You Probably Already Are Even If You Don’t Know) What’s
- the difference between
- TLS and SSL?
You Should Use TLS and Not SSL
TLS, short for Transport Layer Security, and SSL,
short for Secure Socket Layers, are cryptographic protocols that encrypt data and authenticate a connection when moving data over the Internet
.
For example, if you’re processing credit card payments on your website, TLS and SSL can help you process that data securely so malicious actors can’t get their hands on it.
So, What is the difference between TLS and SSL?
Well, TLS is actually just a newer version of SSL. Fixes some security vulnerabilities in the above SSL protocols.
Before we learn more about the details, it’s important to understand the basic history of SSL and TLS.
SSL 2.0
was first released in February 1995 (SSL 1.0 was never released publicly due to security flaws). Although SSL 2.0 was released publicly, it also contained security flaws and was quickly replaced by SSL 3.0 in 1996.
Then, in 1999, the first version of TLS (1.0) was released as an upgrade to SSL 3.0. Since then, there have been three more versions of TLS, with the most recent version being TLS 1.3 in August 2018.
At this point, both public versions of SSL have been deprecated and have known security vulnerabilities (more on this later).
Here is the complete history of SSL and TLS versions:
SSL
- 1.0: Never released publicly due to security concerns. SSL
- 2.0 – released in 1995. Deprecated in 2011. You have known security issues.
- SSL 3.0 – released in 1996. Deprecated in 2015. You have known security issues.
- TLS 1.0 – released in 1999 as an upgrade to SSL 3.0. Deprecation planned in 2020.
- TLS 1.1 – released in 2006. Deprecation planned in 2020.
- TLS 1.2 – released in 2008.
- TLS 1.3 – released in 2018.
How do TLS and SSL work to protect
data?
This is the high-level process on how SSL
and TLS work.
When you install an SSL/TLS certificate on your web server (often simply called an “SSL certificate”), it includes a public key and a private key that authenticate your server and allow your server to encrypt and decrypt data.
When a visitor goes to your site, their web browser will look for your site’s SSL/TLS certificate. The browser will then perform a “handshake” to verify the validity of your certificate and authenticate your server. If the SSL certificate is invalid, your users may face the “your connection is not private” error, which could cause them to leave your website.
Once a visitor’s browser determines that their certificate is valid and authenticates their server, it essentially creates an encrypted link between it and your server to transport data securely.
This is also where HTTPS comes in (HTTPS stands for “HTTP over SSL/TLS”).
HTTP,
and the more recent HTTP/2, are application protocols that play an essential role in transferring information over the Internet.
With simple HTTP, that information is vulnerable to attack. But when you use HTTP over SSL or TLS (HTTPS), you encrypt and authenticate that data during transport, making it secure.
This is why you can securely process credit card details over HTTPS but not over HTTP, and also why Google Chrome is pushing so hard for HTTPS adoption.
Why is it called an SSL certificate if SSL is deprecated?
Previously, you learned that TLS is the latest version of SSL and that both public versions of SSL have been deprecated for several years and contain known security vulnerabilities.
That might make you wonder: why is it called an SSL certificate and not a TLS certificate? After all, TLS is the modern security protocol.
For example, if you search Kinsta’s feature page, you’ll see that Kinsta advertises a free SSL certificate, not a free TLS certificate.
Don’t worry: Kinsta isn’t using outdated technology!
No, the reason most people still refer to them as SSL certificates is basically a branding issue. Most major certificate providers still refer to certificates as SSL certificates, so the naming convention persists.
In reality, all of the “SSL Certificates” you see advertised are actually SSL/TLS Certificates (which include the free SSL certificates we offer as part of our Cloudflare integration).
That is, you can use SSL and TLS protocols with your certificate.
There is no such thing as just an SSL certificate or just a TLS certificate,
and you don’t need to worry about replacing your SSL certificate with a
TLS certificate.
Should I use TLS or SSL? Is TLS
replacing SSL?
Yes, TLS is replacing SSL. And yes, you should use TLS instead of SSL.
As you learned earlier, both public versions of SSL are deprecated in large part due to known security vulnerabilities in them. As such, SSL is not a fully secure protocol in 2019 and beyond.
TLS, the most modern version of SSL, is secure. In addition, recent versions of TLS also offer performance benefits and other improvements.
Not only is TLS more secure and efficient, but most modern web browsers no longer support SSL 2.0 and SSL 3.0. For example, Google Chrome stopped supporting SSL 3.0 in 2014, and most major browsers plan to stop supporting TLS 1.0 and TLS 1.1 in 2020.
In fact, Google started showing warning notifications ERR_SSL_OBSOLETE_VERSION in Chrome.
So how do you make sure you’re using the latest versions of TLS and not older, insecure SSL protocols?
First of all, remember that your certificate is not the same as the protocol your server uses. You do not need to change the certificate to use TLS. Although it might be marked as an “SSL certificate,” your certificate already supports SSL and TLS protocols.
Instead, you control which protocol your website uses at the server level.
If you’re hosting on Kinsta, Kinsta already enables TLS 1.3 for you, which is the most modern, secure, and high-performance version, as well as TLS 1.2.
If you’re hosting elsewhere, you can use the SSL Labs tool to check which protocols are enabled for your site.
For example, if you test a website hosted on Kinsta, you can see how Kinsta enables TLS 1.2 and TLS 1.3 but disables older, insecure versions of SSL:
<img src="https://kinsta.com/wp-content/uploads/2019/12/kinsta-supported-tls-versions.jpg" alt="How to test which SSL/
If you find that your server still supports outdated SSL protocols, you can contact your host’s support for help or follow these instructions to disable SSL on the two most popular web servers (Apache and
Nginx): Disable outdated SSL versions on the Apache web server
- Disable outdated SSL versions on
- Nginx web server
the
Why does Kinsta enable multiple TLS protocols?
If TLS 1.3 is the most modern and highest-performing protocol, why does Kinsta bother to enable the slightly older TLS 1.2 protocol as well?
In other words: what is the benefit of having multiple protocols enabled?
As you learned earlier, there are two parts to the SSL/TLS handshake:
- Your
- The client (usually a visitor’s web browser)
web server
For the
handshake to work, both must support the same protocol
.
Therefore, the main benefit of having multiple protocols is compatibility
. For example, while Chrome and Firefox added support for TLS 1.3
almost immediately after their release in 2018, it took a little longer for Apple and Microsoft to add TLS 1.3 support.
Even in 2019, the following browsers still lack support
TLS 1.3: Internet
- Explorer
- Mini
- UC Browser Mobile Opera
- for Android
- Samsung Internet
- Baidu Browser
Opera
Browser Android
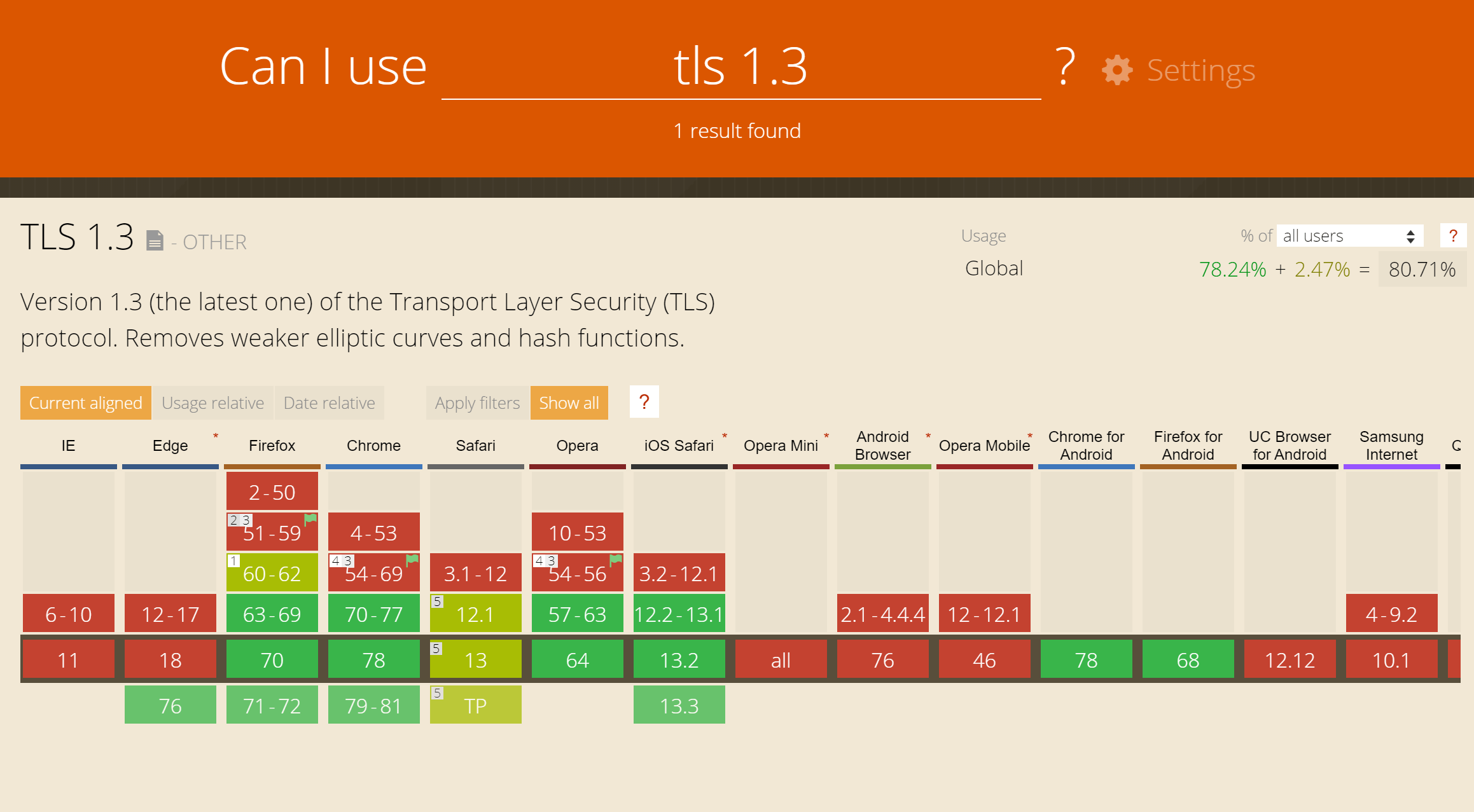 TLS 1.3 web browser support
TLS 1.3 web browser support
But while TLS 1.3 is yet to have full adoption, all major browsers support TLS
in 2019:
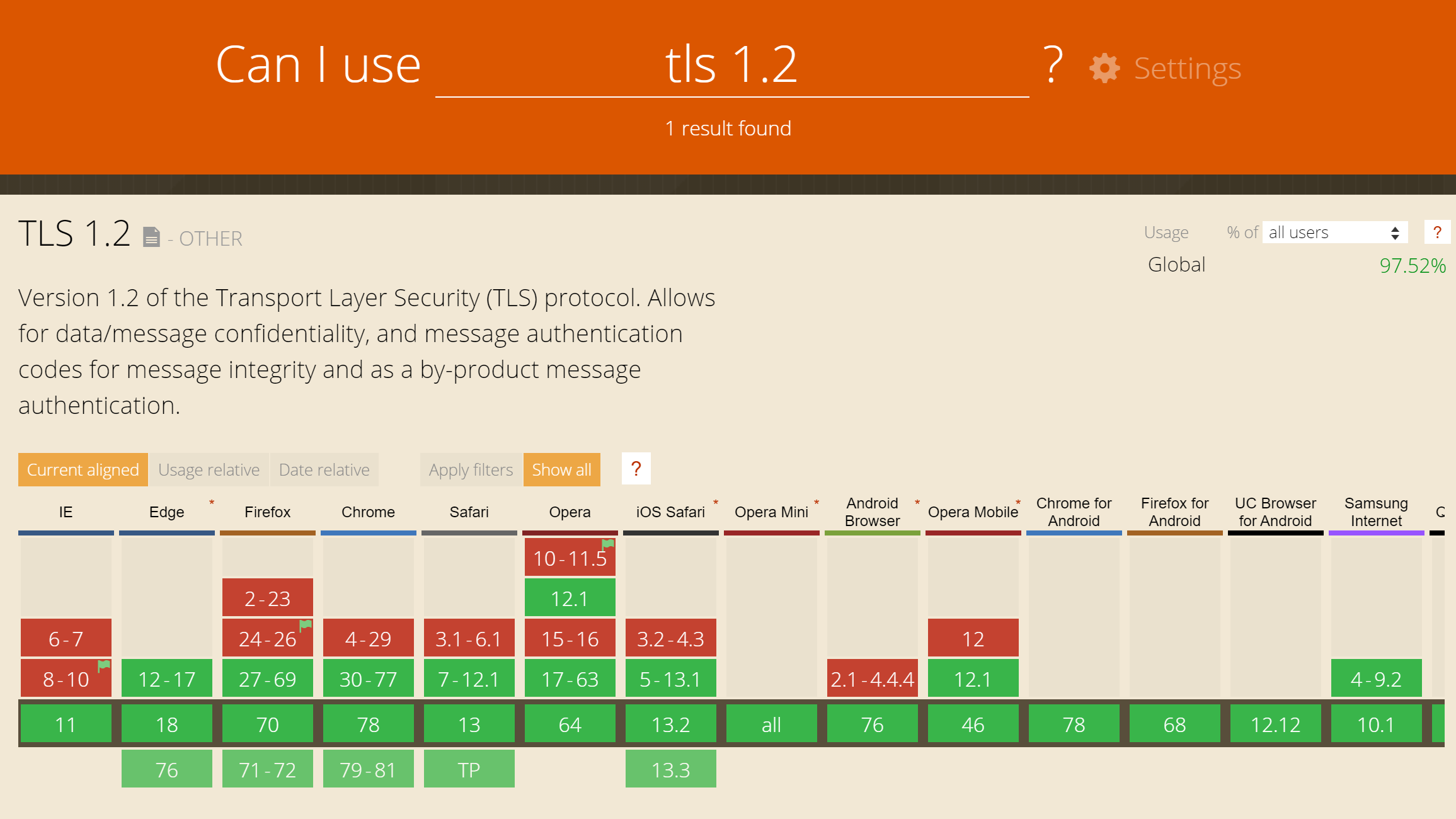 TLS 1.2 web browser support By having TLS 1.3 and TLS 1.2 enabled on your server, you can ensure compatibility no matter what, while also getting the benefits of
TLS 1.2 web browser support By having TLS 1.3 and TLS 1.2 enabled on your server, you can ensure compatibility no matter what, while also getting the benefits offor browsers that support it, such as Chrome and Firefox.
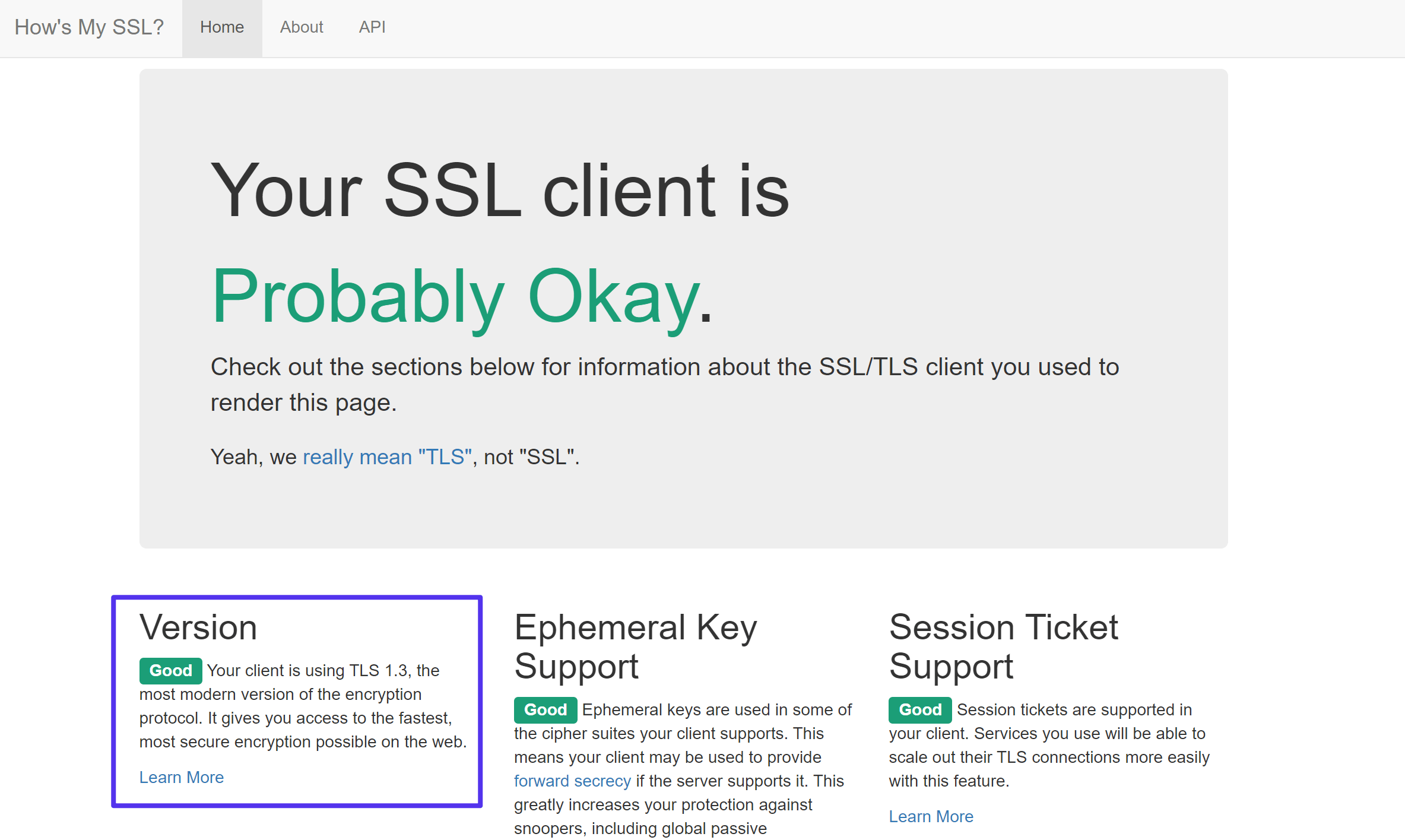
If you want to check which version of SSL/TLS your web browser is using, you can use the How is My SSL tool:
When it comes to security, you see SSL, TLS, HTTPS everywhere… And you might get lost. What do all these acronyms mean? Here are all the answers you need! 🔐😀Click To Tweet
Summary To
sum it all up, TLS and SSL
are protocols for authenticating and encrypting data transfer on the
Internet.
The two are closely linked and TLS is really the most modern and secure version of SSL.
While SSL is still the dominant term on the internet, most people really mean TLS when they say SSL, because both public versions of SSL are insecure and have long since become obsolete.
To use the SSL and TLS protocols, you need to install a certificate on your server (here’s how to install an SSL certificate in WooCommerce). Again, although most people refer to these as “SSL certificates,” these certificates support both SSL and TLS protocols.
You don’t need to worry about “changing” your SSL certificate into a TLS certificate. If you have already installed an “SSL certificate”, you can be sure that it also supports TLS.
It’s important to use the latest versions of TLS because SSL is no longer secure, but your certificate doesn’t determine the protocol your server uses. Instead, once you have a certificate, you can choose which protocols to use at a server level.
If you’re hosting on Kinsta, Kinsta currently enables TLS 1.2 and TLS 1.3, all of which are secure and compatible with all major browsers.
