Linux is often regarded as one of the most secure platforms that is reliable and high performance. It comes with several tricks to offer a safe yet robust environment. One such feature is SELinux (Security-Enhanced Linux). It is a kernel-level security architecture that allows the system administrator to have more control over who accesses the computer.
In the case of RHEL/CentOS, the SELinux feature is enabled by default. For security reasons, it is recommended to stay enabled. However, in certain situations, you may need to disable it. For example, not all applications can function correctly when SELinux is enabled. In such a case, you may want to disable SELinux.
See how to disable SELinux on CentOS.
Disabling SELinux SELinux
has an interesting origin history. It was first developed by the United States National Security Agency, also known as NSA as a patch for the Linux kernel using Linux security modules. It was released to the open source community in 2000. SELinux was integrated as part of the Linux kernel starting in 2003.
There are two types of SELinux disablement. It is possible to disable SELinux temporarily or permanently. Depending on what your situation needs, follow the appropriate method. Note that the system is relatively more vulnerable when SELinux is disabled, so think twice before making the switch.
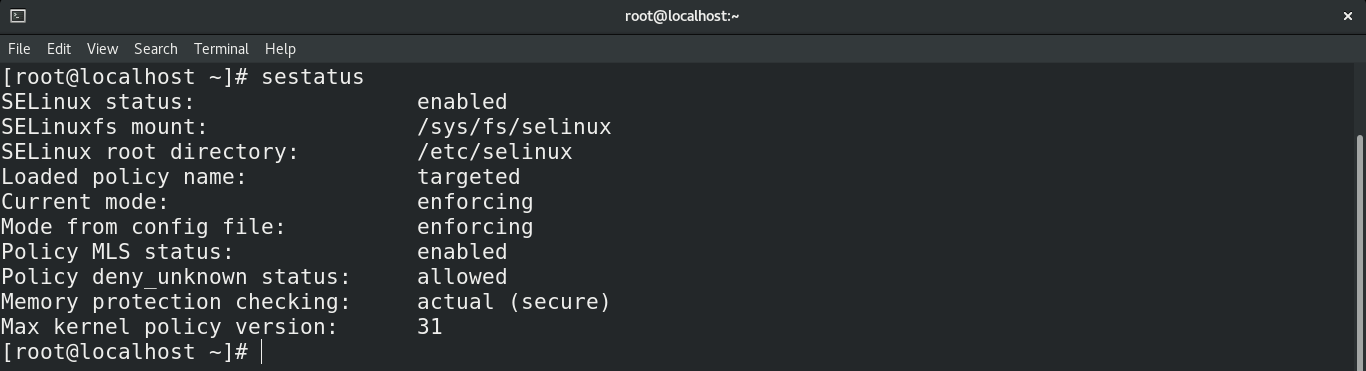
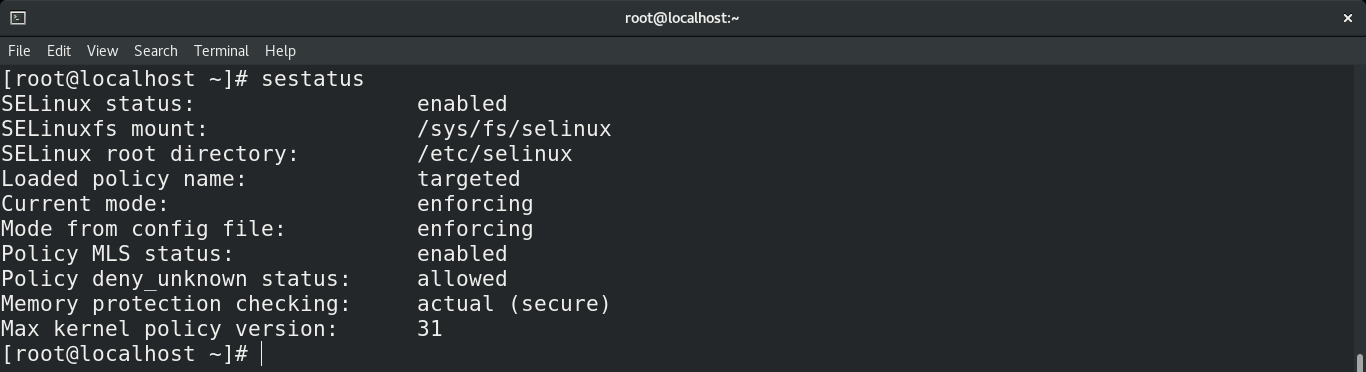
Checking
SELinux status
First, check the status of SELinux. Run the following command.
temporary SELinux disable
The following procedures will disable SELinux temporarily. Once the system boots, it will revert to the default SELinux settings.
The setenforce command is the default tool for setting the SELinux state. If you configure SELinux mode using setenforce, then you do not have to reboot the system. Run the following command to set SELinux to permissive.
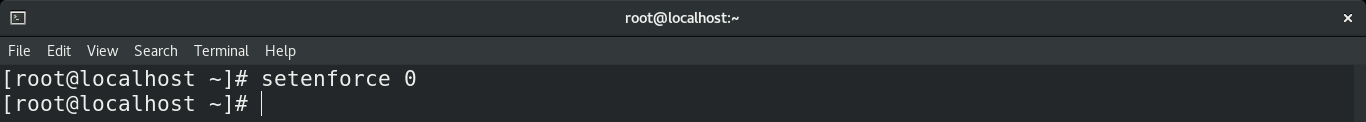
Instead of using the numeric value, you can also use the alternative term “Permissive”.
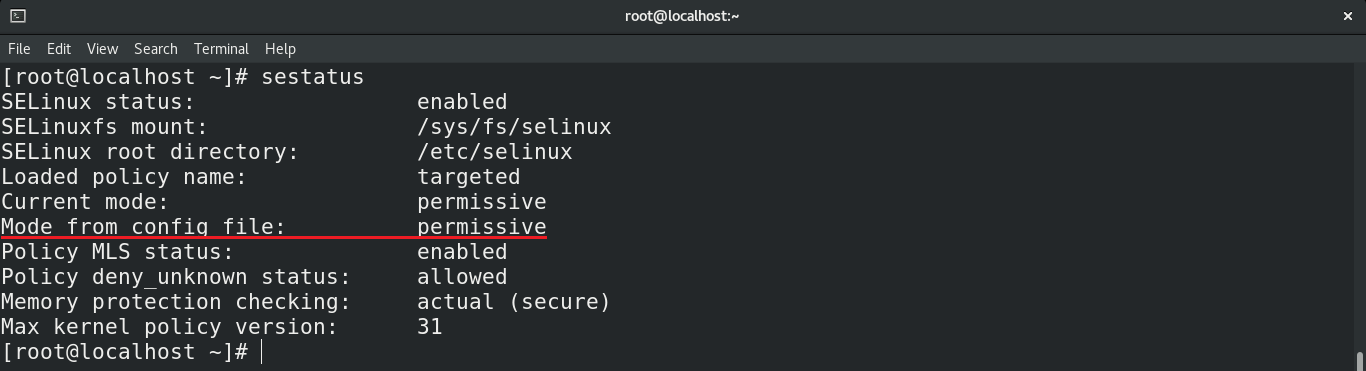
 Check the
Check the
output of the setenforce command. <img src
=”https://linuxhint.com/wp-content/uploads/2020/11/image5.png”
alt=”” /> Another way is to manually edit the SELinux configuration file. Open the file in your favorite text editor. I’ll open it on Vim.
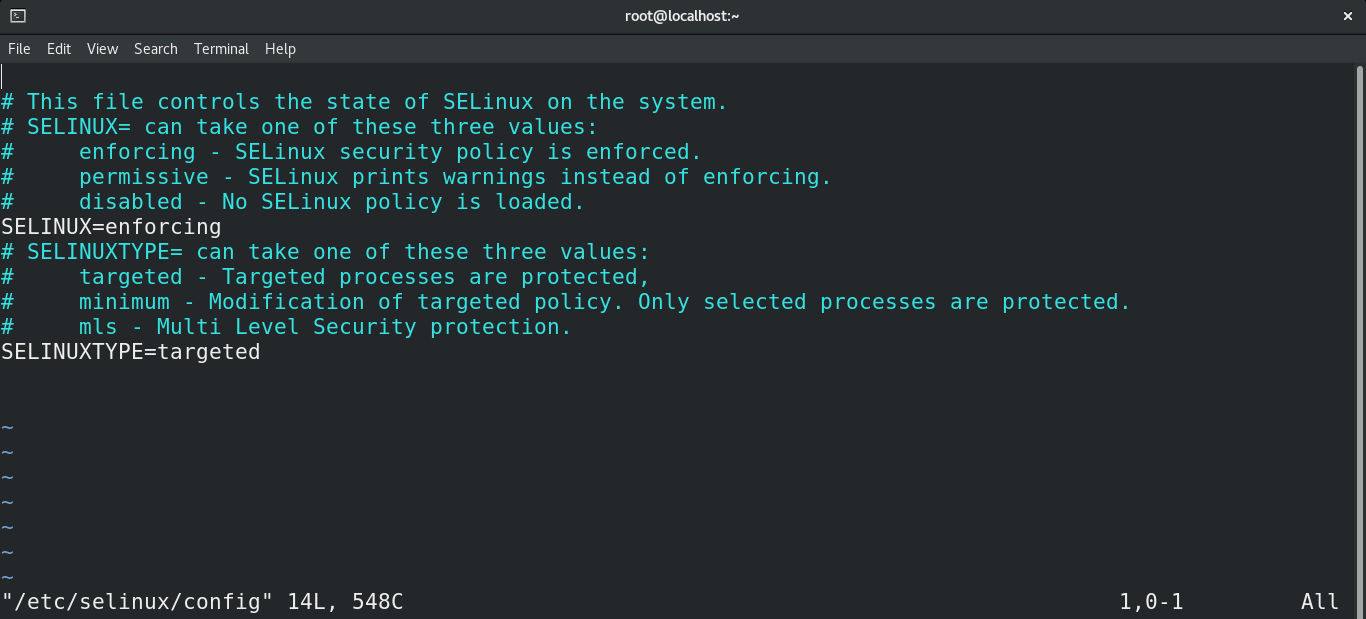
Change the value from “SELINUX” to permissive. <img src
=”https://linuxhint.com/wp-content/uploads/2020/11/image7.png”
alt=”” /> Save the file. You may want to restart the system after you make this change. Check the result of editing the configuration file.
permanent SELinux disable
This method will disable SELinux permanently. To enable SELinux again, you must manually roll back the changes made in this method.
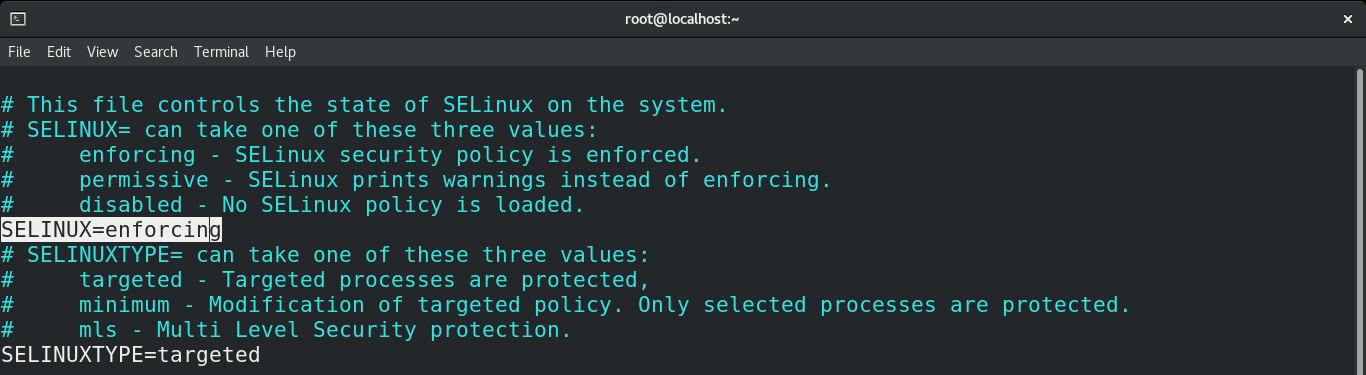
Open the SELinux configuration file with your favorite text editor. In my case, I will use Vim.
Here, the variable “SELINUX” determines the state of SELinux. As you can see, there are three possible scroll down to the variable “SELINUX” and change its value to “disabled”.
 Save the file and close the editor. The system needs a restart for the changes to take effect. After rebooting, check the status of SELinux.
Save the file and close the editor. The system needs a restart for the changes to take effect. After rebooting, check the status of SELinux.

Enabling
SELinux Need to enable SELinux again? Depending on the method you followed, the way to enable SELinux will be different.
First, temporary deactivation. If you used the setenforce command to disable SELinux, a simple system restart will return the SELinux state to default values. If restarting is not an option, use the setenforce command again to manually reassign the value.

As we have seen above, it is also possible to use an alternative value with setenforce . <img src
=”
https://linuxhint.com/wp-content/uploads/2020/11/image10.png” alt=”” /> If you have manually edited the SELinux configuration file, you must manually revert it. Open the configuration file in a text editor.
Set the value of “SELINUX” back to “forcing”. Then, save the file and restart the system.
Check the status of SELinux to verify the changes
.
Final thought
Disabling SELinux is a very simple task. This method should also work with other distributions that have SELinux support.
Interested in making your system more secure? Then refer to the Linux security hardening checklist. It should act as a quick but useful introduction to the world of Linux security.
Happy computing!